Information Technology (IT) and Operational Technology (OT) are different in a lot of ways, from their design to their maintenance workflows and more. When IT and OT merge, these differences create all new challenges for cybersecurity.
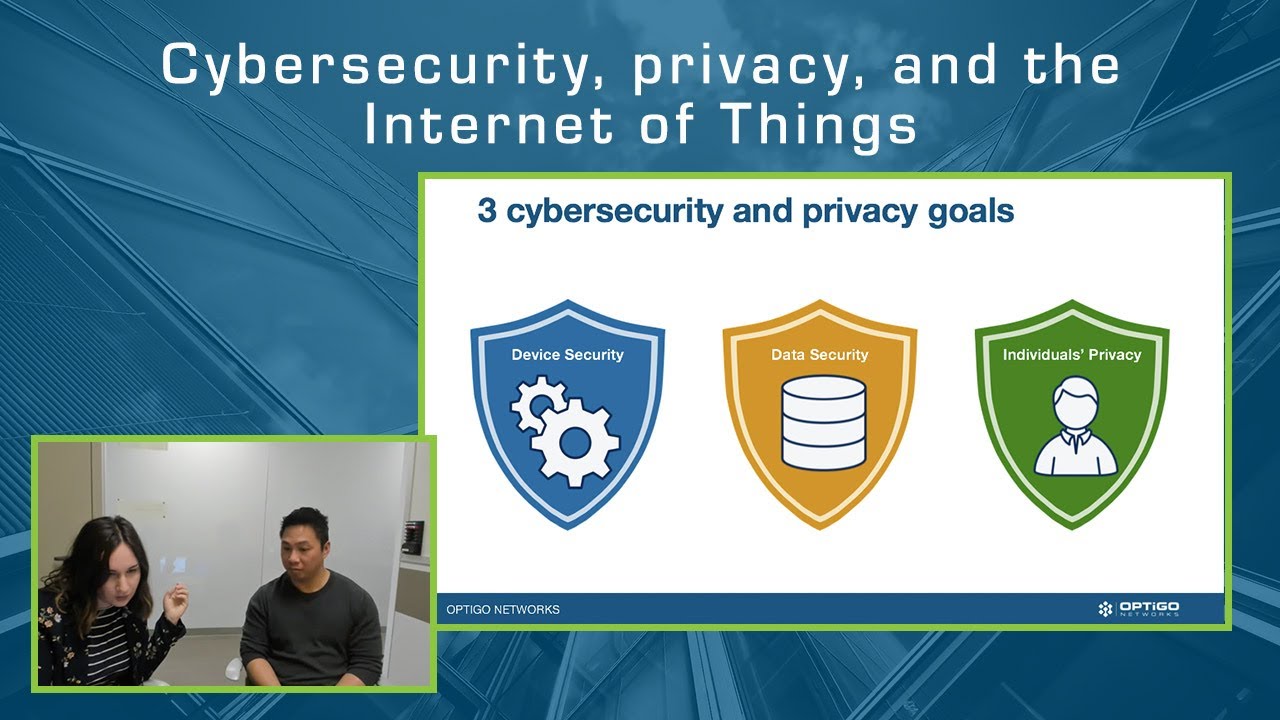
IT has standards for protecting device security, data security, and people’s privacy, but these standards do not make sense for many connected OT devices. In IT, for example, cybersecurity vulnerabilities are the absolute top priority. In OT, operations are the top priority, while network security is a close second. Ensuring the building is still functioning as expected is critical to maintain physical safety and security, before addressing a network vulnerability.
Last year, the National Institute of Standards and Technology (NIST) released the report “Considerations for Managing Internet of Things (IoT) Cybersecurity and Privacy Risks,” exploring these exact differences and cybersecurity threats. The report is an in-depth analysis of current threats and how IoT devices can or cannot meet those threats head-on.
This is a huge opportunity to pull in your IT counterpart and collaborate on cybersecurity standards that make sense for your connected OT devices.
Join us for a one-hour webinar digging into the report, where we’ll summarize what IT and OT teams on the ground should know about their systems and security. We’ll dig into top risks identified in the report, challenges for securing the Internet of Things, and NIST’s recommendations.
Date: February 25th, 2020
Time: 11:30 a.m. PDT / 2:30 p.m. EDT